Cloud and edge networks are establishing a brand new line of protection, known as confidential computing, to guard the rising wealth of knowledge customers course of in these environments.
Confidential Computing Outlined
Confidential computing is a approach of defending knowledge in use, for instance whereas in reminiscence or throughout computation, and stopping anybody from viewing or altering the work.
Utilizing cryptographic keys linked to the processors, confidential computing creates a trusted execution atmosphere or safe enclave. That secure digital house helps a cryptographically signed proof, known as attestation, that the {hardware} and firmware is accurately configured to forestall the viewing or alteration of their knowledge or utility code.
Within the language of safety specialists, confidential computing offers assurances of knowledge and code privateness in addition to knowledge and code integrity.
What Makes Confidential Computing Distinctive?
Confidential computing is a comparatively new functionality for safeguarding knowledge in use.
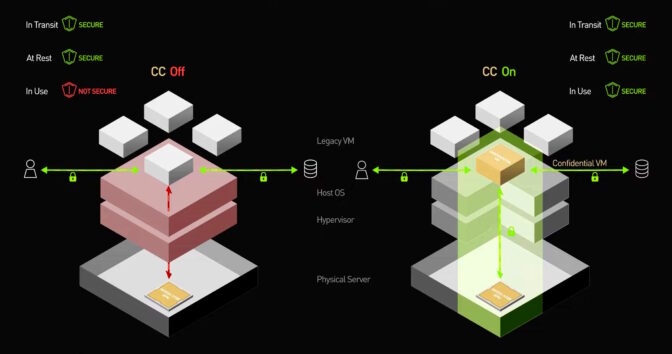
For a few years, computer systems have used encryption to guard knowledge that’s in transit on a community and knowledge at relaxation, saved in a drive or non-volatile reminiscence chip. However with no sensible approach to run calculations on encrypted knowledge, customers confronted a danger of getting their knowledge seen, scrambled or stolen whereas it was in use inside a processor or important reminiscence.
With confidential computing, programs can now cowl all three legs of the data-lifecycle stool, so knowledge isn’t within the clear.

Prior to now, pc safety primarily centered on defending knowledge on programs customers owned, like their enterprise servers. On this situation, it’s okay that system software program sees the person’s knowledge and code.
With the appearance of cloud and edge computing, customers now routinely run their workloads on computer systems they don’t personal. So confidential computing flips the main target to defending the customers’ knowledge from whoever owns the machine.
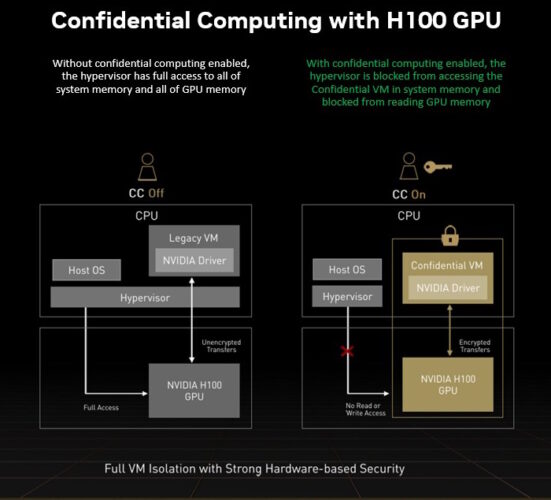
With confidential computing, software program operating on the cloud or edge pc, like an working system or hypervisor, nonetheless manages work. For instance, it allocates reminiscence to the person program, however it will probably by no means learn or alter the info in reminiscence allotted by the person.
How Confidential Computing Received Its Title
A 2015 analysis paper was one in every of a number of utilizing new Safety Guard Extensions (Intel SGX) in x86 CPUs to indicate what’s attainable. It known as its method VC3, for Verifiable Confidential Cloud Computing, and the title — or not less than a part of it — caught.
“We began calling it confidential cloud computing,” stated Felix Schuster, lead creator on the 2015 paper.
4 years later, Schuster co-founded Edgeless Methods, an organization in Bochum, Germany, that develops instruments so customers can create their very own confidential-computing apps to enhance knowledge safety.
Confidential computing is “like attaching a contract to your knowledge that solely permits sure issues to be completed with it,” he stated.
How Does Confidential Computing Work?
Taking a deeper look, confidential computing sits on a basis known as a root of belief, which relies on a secured key distinctive to every processor.
The processor checks it has the precise firmware to begin working with what’s known as a safe, measured boot. That course of spawns reference knowledge, verifying the chip is in a identified secure state to begin work.
Subsequent, the processor establishes a safe enclave or trusted execution atmosphere (TEE) sealed off from the remainder of the system the place the person’s utility runs. The app brings encrypted knowledge into the TEE, decrypts it, runs the person’s program, encrypts the consequence and sends it off.
At no time might the machine proprietor view the person’s code or knowledge.
One different piece is essential: It proves to the person nobody might tamper with the info or software program.
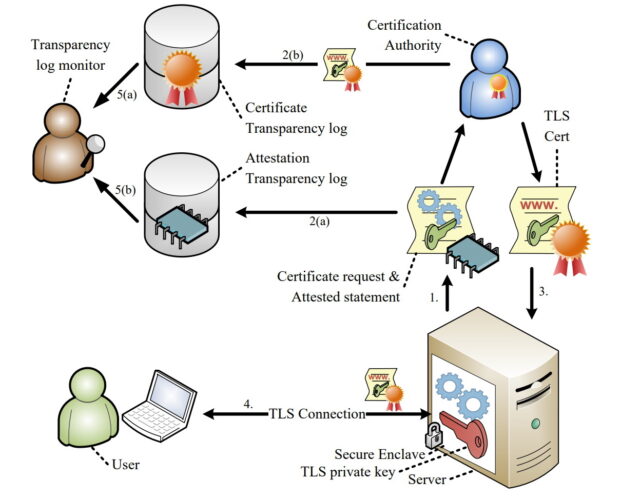
The proof is delivered by way of a multi-step course of known as attestation (see diagram above).
The excellent news is researchers and commercially accessible providers have demonstrated confidential computing works, typically offering knowledge safety with out considerably impacting efficiency.
Shrinking the Safety Perimeters
Consequently, customers not have to belief all of the software program and programs directors in separate cloud and edge firms at distant places.
Confidential computing closes many doorways hackers like to make use of. It isolates packages and their knowledge from assaults that would come from firmware, working programs, hypervisors, digital machines — even bodily interfaces like a USB port or PCI Specific connector on the pc.
The brand new stage of safety guarantees to cut back knowledge breaches that rose from 662 in 2010 to greater than 1,000 by 2021 within the U.S. alone, in response to a report from the Identification Theft Useful resource Middle.
That stated, no safety measure is a panacea, however confidential computing is a good safety software, putting management instantly within the arms of “knowledge homeowners”.
Use Circumstances for Confidential Computing
Customers with delicate datasets and controlled industries like banks, healthcare suppliers and governments are among the many first to make use of confidential computing. However that’s simply the beginning.
As a result of it protects delicate knowledge and mental property, confidential computing will let teams really feel they will collaborate safely. They share an attested proof their content material and code was secured.
Instance purposes for confidential computing embrace:
- Corporations executing good contracts with blockchains
- Analysis hospitals collaborating to coach AI fashions that analyze tendencies in affected person knowledge
- Retailers, telecom suppliers and others on the community’s edge, defending private data in places the place bodily entry to the pc is feasible
- Software program distributors can distribute merchandise which embrace AI fashions and proprietary algorithms whereas preserving their mental property
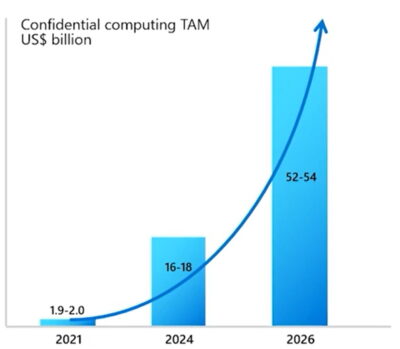
Whereas confidential computing is getting its begin in public cloud providers, it is going to unfold quickly.
Customers want confidential computing to guard edge servers in unattended or hard-to-reach places. Enterprise knowledge facilities can use it to protect towards insider assaults and shield one confidential workload from one other.
To this point, most customers are in a proof-of-concept stage with hopes of placing workloads into manufacturing quickly, stated Schuster.
Wanting ahead, confidential computing won’t be restricted to special-purpose or delicate workloads. Will probably be used broadly, just like the cloud providers internet hosting this new stage of safety.
Certainly, specialists predict confidential computing will grow to be as broadly used as encryption.
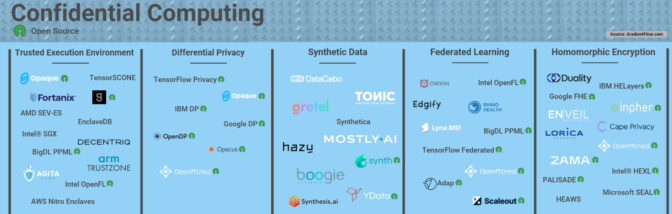
The know-how’s potential motivated distributors in 2019 to launch the Confidential Computing Consortium, a part of the Linux Basis. CCC’s members embrace processor and cloud leaders in addition to dozens of software program firms.
The group’s initiatives embrace the Open Enclave SDK, a framework for constructing trusted execution environments.
“Our greatest mandate is supporting all of the open-source initiatives which are foundational components of the ecosystem,” stated Jethro Beekman, a member of the CCC’s technical advisory council and vice chairman of know-how at Fortanix, one of many first startups based to develop confidential computing software program.
“It’s a compelling paradigm to place safety on the knowledge stage, somewhat than fear concerning the particulars of the infrastructure — that ought to lead to not needing to examine knowledge breaches within the paper each day,” stated Beekman, who wrote his 2016 Ph.D. dissertation on confidential computing.
How Confidential Computing Is Evolving
Implementations of confidential computing are evolving quickly.
On the CPU stage, AMD has launched Safe Encrypted Virtualization with Safe Nested Paging (SEV-SNP). It extends the process-level safety in Intel SGX to full digital machines, so customers can implement confidential computing with no need to rewrite their purposes.
High processor makers have aligned on supporting this method. Intel’s help comes through new Trusted Area Extensions. Arm has described its implementation, known as Realms.
Proponents of the RISC-V processor structure are implementing confidential computing in an open-source challenge known as Keystone.
Accelerating Confidential Computing
NVIDIA is bringing GPU acceleration to VM-style confidential computing to market with its Hopper structure GPUs.
The H100 Tensor Core GPUs allow confidential computing for a broad swath of AI and excessive efficiency computing use instances. This provides customers of those safety providers entry to accelerated computing.
In the meantime, cloud service suppliers are providing providers at the moment primarily based on a number of of the underlying applied sciences or their very own distinctive hybrids.
What’s Subsequent for Confidential Computing
Over time, trade pointers and requirements will emerge and evolve for points of confidential computing comparable to attestation and environment friendly, safe I/O, stated Beekman of CCC.
Whereas it’s a comparatively new privateness software, confidential computing’s capability to guard code and knowledge and supply ensures of confidentiality makes it a robust one.
Wanting forward, specialists anticipate confidential computing might be blended with different privateness strategies like totally homomorphic encryption (FHE), federated studying, differential privateness, and different types of multiparty computing.
Utilizing all the weather of the fashionable privateness toolbox might be key to success as demand for AI and privateness grows.
So, there are a lot of strikes forward within the nice chess recreation of safety to beat the challenges and understand the advantages of confidential computing.
Take a Deeper Dive
To be taught extra, watch “Hopper Confidential Computing: The way it Works Beneath the Hood,” session S51709 at GTC on March 22 or later (free with registration).
Take a look at “Confidential Computing: The Developer’s View to Safe an Utility and Information on NVIDIA H100,” session S51684 on March 23 or later.
You can also attend a March 15 panel dialogue on the Open Confidential Computing Convention moderated by Schuster and that includes Ian Buck, NVIDIA’s vice chairman of hyperscale and HPC. And watch the video beneath.


